Orion.the personal representative.
Represents you to the world. Takes calls, joins meetings, works across your devices, knows your people.
Represents you to the world. Takes calls, joins meetings, works across your devices, knows your people.
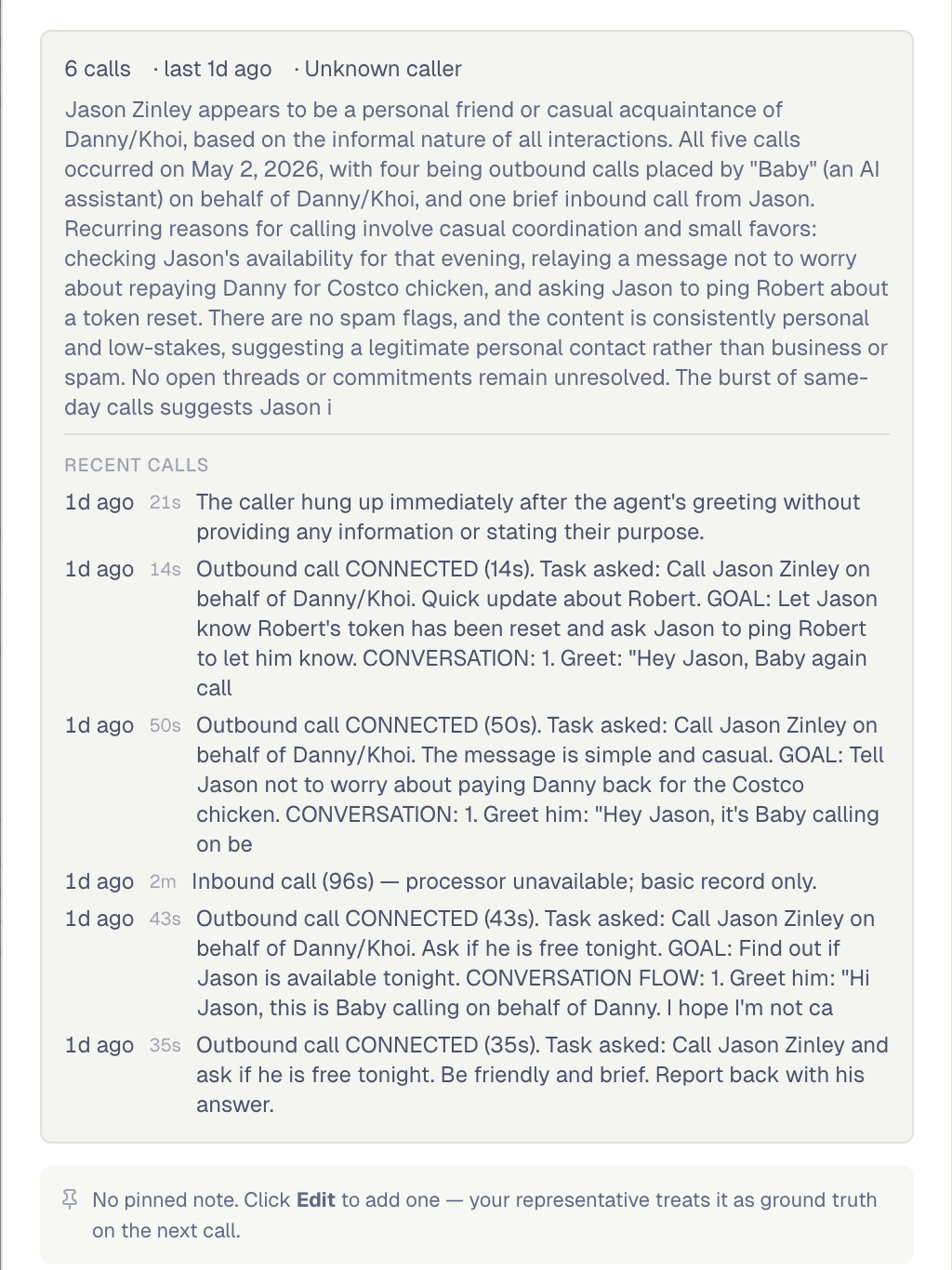
When you can't pick up, Orion does. Nothing falls through, no one's left hanging.
Meet Orion RepresentativeAlready there on whatever you're holding. Walk away from one, keep going on the next.
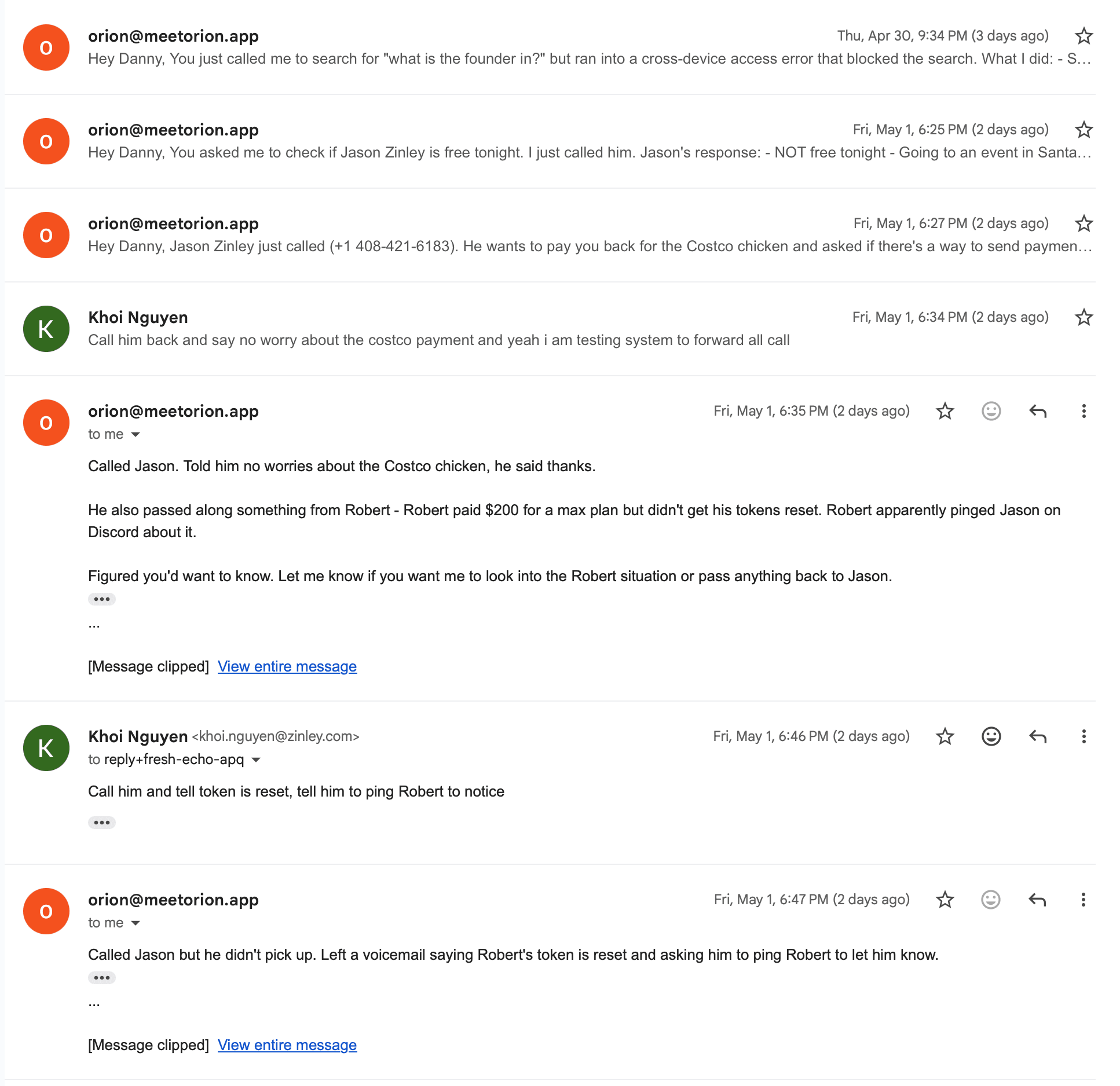
See every deviceYou never repeat yourself. Orion already knows your people, your habits, and where you left off.
Text back, email back, chat back. The work keeps moving without you starting over.
Your calls still get answered, your messages still get handled. Come back to progress, not a pile of missed things.
Books the table. Sits on hold. Replies in your words. You stay in the loop, not in the chair.
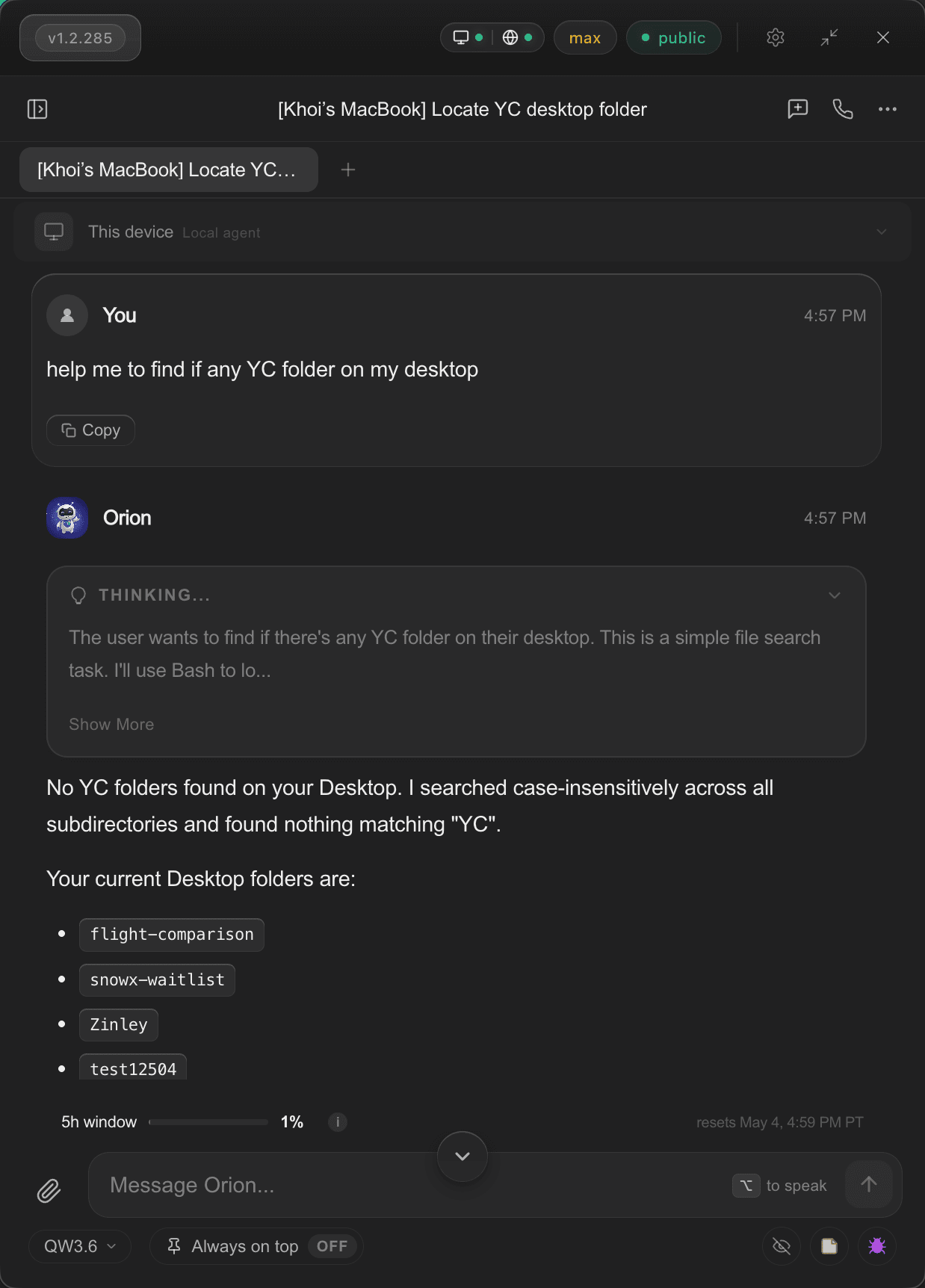
Hand off your work. Orion writes, browses, and gets through the list while you do something else.
And just about anything else. See all the connections →
What I didn't expect: it picks up the same conversation on my laptop that I started on my phone — including the half-finished thought I'd been mumbling at it on the F train. Voice notes underground, then real code at my desk. I keep waiting for the seam and there isn't one.
Mia's school has Orion's number now. They've called it three times this month — pickup change, fundraiser, something about her lunch account. Clean summary text after each. A PTA mom mentioned to me last week that 'my assistant' had been really patient with her. I just nodded.
I've used the same plumber for years — Carlos. He called Orion's line about scheduling and Orion already had him tagged as a family vendor from a previous job, pulled up the last invoice without me asking. Carlos told my husband later it was the easiest scheduling call he'd had all week. That meant something.
A client called Orion's line at 11pm on a Sunday. I was asleep. Orion told them I'd respond in the morning, took notes on what was urgent, and — this is the part I care about — didn't make any promises on my behalf. Monday morning I had a clean brief and the client wasn't waiting. That boundary is the part I trust.
My mom called Orion by accident — she meant to call me. Orion knew her voice, told her I was in a meeting, took her message. She called me back afterward laughing, said it had a nicer phone manner than I do. Probably true.
Pager hit my watch at 1am. Asked Orion from my phone, got the diagnosis lying in bed. Walked to my desk and the laptop was already on the same incident — same logs, same context. It drafted the rollback while I made coffee. I still ran it manually. That's where I am with it.